Thursday, May 17, 2012
CyberSecurity Malaysia launch its own DNSChanger detection page
http://dnschanger.detect.my/
If your PC is clean you will be notice as 'Congratulation!' with green background otherwise you will be detected as red background. They also provided a free removal tools for Mac and Windows users.
Saturday, December 31, 2011
Another Chinese Internet Fraudulent (yhoo-it.com)
From the given shortened URL it will redirect user to the following URL:
http://yhoo-it.com/?id=4ccda25f27843014&s=1&user=matkamil2000
The URL seem to be already expired. But soon it will appeared again. The actual website will appear some kind of offering money that needs user to input their user name and email.
Registration Service Provided By: Bizcn.com
Website: http://www.bizcn.com
Whois Server: whois.bizcn.com
Domain name: yhoo-it.com
Registrant Contact:
zhang yu
yu zhang [email protected]
0463965823 fax: 0463965823
changhailu12hao
nanning guangxi 230254
cn
Administrative Contact:
yu zhang [email protected]
0463965823 fax: 0463965823
changhailu12hao
nanning guangxi 230254
cn
Technical Contact:
yu zhang [email protected]
0463965823 fax: 0463965823
changhailu12hao
nanning guangxi 230254
cn
Billing Contact:
yu zhang [email protected]
0463965823 fax: 0463965823
changhailu12hao
nanning guangxi 230254
cn
DNS:
ns7.cnmsn.net
ns8.cnmsn.net
Created: 2011-12-04
Expires: 2012-12-04
The domain name seem to be newly registered and exactly the time I was start monitoring it. The domain has been pointed to two DNS ns7.cnmsn.net and ns8.cnmsn.net. The DNS server were also registered from China.
Registration Service Provided By: Bizcn.com
Website: http://www.bizcn.com
Whois Server: whois.bizcn.com
Domain name: cnmsn.net
Registrant Contact:
XiaMen Longtop Online Technology Co.,Ltd
huiping yi [email protected]
+865922577888 fax: +865922577111
61, WangHai Road, Longtop Group Building, Xiamen Software Park
xiamen fujian 361008
cn
Administrative Contact:
huiping yi [email protected]
+865922577888 fax: +865922577111
61, WangHai Road, Longtop Group Building, Xiamen Software Park
xiamen fujian 361008
cn
Technical Contact:
huiping yi [email protected]
+865922577888 fax: +865922577111
61, WangHai Road, Longtop Group Building, Xiamen Software Park
xiamen fujian 361008
cn
Billing Contact:
huiping yi [email protected]
+865922577888 fax: +865922577111
61, WangHai Road, Longtop Group Building, Xiamen Software Park
xiamen fujian 361008
cn
DNS:
dns.bizcn.com
dns.cnmsn.net
ns5.cnmsn.net
ns6.cnmsn.net
ns1.4everdns.com
ns2.4everdns.com
Created: 2003-08-08
Expires: 2015-02-27
Well, lets dig some more.
Nmap scan report for yhoo-it.com (109.230.222.53)
Host is up (0.29s latency).
rDNS record for 109.230.222.53: hosted.by.xsserver.eu
Not shown: 986 closed ports
PORT STATE SERVICE VERSION
25/tcp filtered smtp
80/tcp open http nginx 1.0.4
|_http-title: Site doesn't have a title (text/html).
|_http-methods: No Allow or Public header in OPTIONS response (status code 405)
111/tcp open rpcbind 2 (rpc #100000)
135/tcp filtered msrpc
139/tcp filtered netbios-ssn
443/tcp open ssh OpenSSH 5.5p1 Debian 6 (protocol 2.0)
| ssh-hostkey: 1024 6e:96:96:b1:aa:4b:e2:1a:e5:9f:35:9c:6a:79:af:df (DSA)
|_2048 48:bb:c1:d4:bf:08:4d:c6:41:30:ea:57:3e:eb:fe:19 (RSA)
445/tcp filtered microsoft-ds
593/tcp filtered http-rpc-epmap
1026/tcp filtered LSA-or-nterm
1027/tcp filtered IIS
4444/tcp filtered krb524
5432/tcp open postgresql PostgreSQL DB 8.4.1 - 8.4.4
6129/tcp filtered unknown
6580/tcp open parsec-master?
Device type: general purpose|WAP|router
Running (JUST GUESSING): Linux 2.6.X|2.4.X (95%), Linksys Linux 2.4.X (92%), Netgear embedded (92%), D-Link embedded (92%), Linksys embedded (92%), Peplink embedded (92%)
, Asus Linux 2.6.X (91%)
Aggressive OS guesses: Linux 2.6.23 - 2.6.33 (95%), Linux 2.6.35 (94%), Linux 2.6.31 (94%), Linux 2.6.32 (94%), Linux 2.6.22 (94%), OpenWrt White Russian 0.9 (Linux 2.4.3
0) (92%), Linux 2.6.18 - 2.6.27 (92%), Linux 2.6.31 - 2.6.34 (92%), Linux 2.6.34 (92%), Netgear DG834G WAP (92%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 9 hops
Service Info: OS: Linux
TRACEROUTE (using port 23/tcp)
HOP RTT ADDRESS
1 12.00 ms 60.53.173.202
2 16.00 ms 60.53.173.213
3 16.00 ms 60.53.173.213
4 228.00 ms 10.55.192.38
5 229.00 ms 10gigabitethernet1-3.core1.lax1.he.net (206.223.123.37)
6 290.00 ms 10gigabitethernet4-3.core1.nyc4.he.net (72.52.92.225)
7 333.00 ms 10gigabitethernet1-2.core1.lon1.he.net (72.52.92.242)
8 399.00 ms 10gigabitethernet4-2.core1.fra1.he.net (184.105.213.146)
9 290.00 ms hosted.by.xsserver.eu (109.230.222.53)
Since I don't trust any source from China even their web hosting provider, I make some Nmap scanning to seem what its got. The web server seem to be running on Unix machine with several web services port opened.
The Yahoo Messenger online status is coming from the expired phone number which probably has been taken by China scammer that live in Malaysia. Malaysia has multicultural country and it's not impossible that a Chinese from China can disguise as Chinese from Malaysia. Another thing is that probably the YM account has been stolen from his machine via malware infection.
More updates coming up soon.
Friday, November 4, 2011
Revoking Trust in DigiCert by Certificate Authority
Issue
Entrust, Inc., a certificate authority in Mozilla’s root program, has informed us that one of their subordinate CAs, the Malaysian company DigiCert Sdn. Bhd, has issued 22 certificates with weak keys. While there is no indication they were issued fraudulently, the weak keys have allowed the certificates to be compromised. Furthermore, certificates from this CA contain several technical issues. They lack an EKU extension specifying their intended usage and they have been issued without revocation information.
This is not a Firefox-specific issue. Nevertheless, given our concerns about the technical practices of this certificate authority, we intend to revoke trust in the DigiCert Sdn. Bhd. intermediate certificate authority.
DigiCert Sdn. Bhd is a Malaysian subordinate CA under Entrust and Verizon (GTE CyberTrust). It bears no affiliation whatsoever with the US-based corporation DigiCert, Inc., which is a member of Mozilla’s root program.
Impact
An attacker could use one of these weak certificates to impersonate the legitimate owners. This could deceive users into trusting websites or signed software appearing to originate from these owners, but actually containing malicious content or software. The certificates in question were issued to a mix of Malaysian government websites and internal systems. We do not believe other sites are at risk.
Status
Mozilla is revoking trust in all certificates issued by DigiCert Sdn. Bhd. and the update will be in Firefox 8 and Firefox 3.6.24. Entrust has issued their own statement on the subject.
Credit
The issue was reported to us by Entrust, Inc.
Source: http://blog.mozilla.com/security/2011/11/03/revoking-trust-in-digicert-sdn-bhd-intermediate-certificate-authority/
Tuesday, April 26, 2011
New Version of Stuxnet 'Stars' Reported
After being investigated from most resources, I was unable to find the sample and strong news about related story. At this moment, I just consider that it is a hoax.
News related:
http://www.f-secure.com/weblog/
http://blogs.csoonline.com/1483/after_stuxnet_a_star_is_born
http://www.google.com.my/search?um=1&hl=en&prmdo=1&biw=1138&bih=519&q=%27stars%27%20stuxnet&ie=UTF-8&sa=N&tab=iw
Thursday, April 14, 2011
The 5th annual Counter-eCrime Operations Summit (CeCOS V)
The fifth annual Counter-eCrime Operations Summit (CeCOS V) will engage questions of operational challenges and the development of common resources for the first responders and forensic professionals who protect consumers and enterprises from the ecrime threat every day. This year's meeting will focus on the development of response paradigms and resources for counter-ecrime managers and forensic professionals. Presenters will proffer case studies of national and regional economies under attack, narratives of successful trans-national forensic cooperation as well as models for cooperation and unified response against ecrime and data resources for forensic activities.

The program will be spread across a three-day conference event on April 27, 28 and 29 in Kuala Lumpur, Malaysia at the Crown Plaza Hotel. The APWG believes under-appreciated operational issues are important enough to be the focus of a conference dedicated exclusively to them. They're often talked about as sidelights but rarely addressed directly as an organizational imperative for the entire counter-ecrime community. CeCOS V makes those operational issue the central focus of the program for the benefit of all ecrime fighters.
References:
http://www.antiphishing.org/events/2011_opSummit.html
Tuesday, April 5, 2011
Zeus source code leaked
At the time I was writing this blog, there is no sign that people already crack the password. This could be dangerous once the password is cracked especially when it's fall into a wrong hand.
UPDATE - 06/04/2011
The source code seem to be already posted at r00tw0rm.com which is currently down due to the missing file.
The CMS they are using is probably vBulletin which is contain missing file.
Tuesday, February 22, 2011
VERA: Reverse Engineering Malware in Visualize
VERA is a visualization tool for reverse engineer to produce a nice view and made easy to understand of program behavior. The latest version so far is v0.31 and can be download it from here. Setting up this tools probably a bit complicated if you got no experiences. Just follow the instruction manual and you should be fine.
References:
http://www.offensivecomputing.net/?q=node/1687
http://www.pentestit.com/2010/12/23/update-vera-v03/
http://ether.gtisc.gatech.edu/source.html
Friday, December 17, 2010
"My Team Pest Control" - Malaysia Real World Scam?
MY TEAM PEST CONTROL
L21A-204, Jalan Cheras PSN,
Pandan 4, Pandan Jaya,
55100 Kuala Lumpur
Tel: 019-364 4157, 03-92812914
Sunday, September 26, 2010
Facebook still can't recognize URL!
Just been testing on few web browser including latest Internet Explorer, FireFox and Chrome. All does same and absolutely not coming from web browser application. In fact, this is part of Facebook programming mistake.
Wednesday, September 1, 2010
Independence Day Web Defacement!
http://ly.my/na
Wednesday, August 11, 2010
Embedded Script on Images file allowed Arbitrary Code Execution
The interesting part, the PNG image file (or what ever image format) is still valid and can be viewed as normal if user did not rename it into .HTA extension. In worst cases, all the script can be obfuscate to make it more undetectable from antivirus software or at least user can't see there is a script in it.
It seem none of antivirus detecting it as I got report from VirusTotal >> http://ly.my/lq
Wednesday, June 30, 2010
Twitter controlled by non-human!
Non of the listed user name above can be pronounces and all their follower and following user are almost equal to each other no wonder whenever user trying to access their account and twitter will said 'Twitter is over capacity. Too many tweets!'. It is not impossible soon twitter could be medium of threat since their API is flexible.
Thursday, March 25, 2010
Youtube down?


p/s: Maybe youtube hired a practical student to take care the rest of PHP service and try their hello world pages.. LoL..
Wednesday, November 11, 2009
iPhone Worm - Ikee
During infection, this little worm will change victim wallpaper to Rick Astley image (80's singer). The worm has been written by Ashley Town a 21 years old unemployed programmer from Wollogong, Australia.
More detail report can be found here.
Thursday, October 15, 2009
New Portable Antivirus on few final stage!
+ New name; now it is Data0.Net Portable Antivirus.
+ Better system tray icon & pop up message.
+ Support multi language including Bahasa Melayu.
+ Speed up database reading for fast scanning.
Friday, October 2, 2009
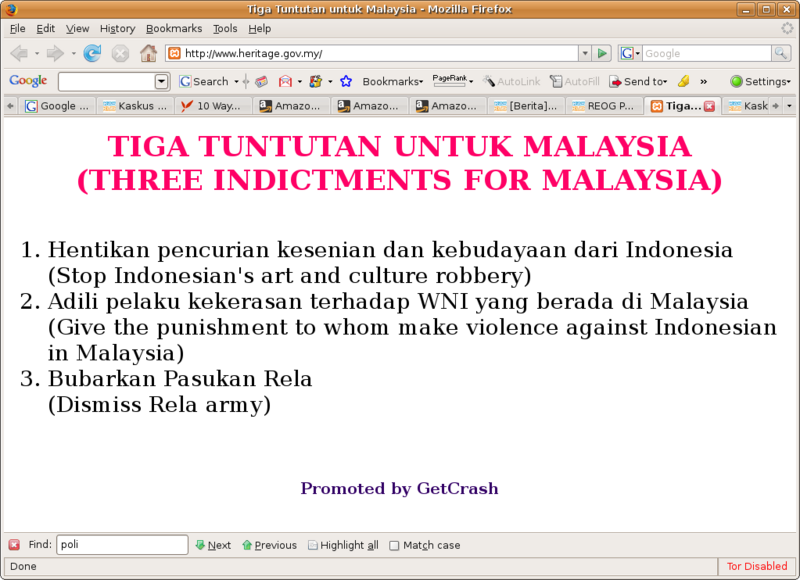
Cyber-Communalism
Internet alone we can find so many articles, libel, forum, blog and many more about this issue (Example 1). Wikipedia also has been describe details about Communalism. This will give impact to all Asian country especially between Malaysia and Indonesia. As an example below show you many website from Malaysia has been defaced because of this issue:
Most of this issue produced by local/foreign media making the conflict more complicated and people will think different and negative perception each other by just read or hearing rumors. As I wrote this topic, there was the latest hot issue such as Pendet dance and Island. While the real thing is, there is none of this issue are truth.
Wednesday, May 6, 2009
New Microsoft Windows 7 RC Launch!
 Just a few minutes ago, I've read google news that Microsoft is already launch a new Microsoft Windows 7 Release Candidate (RC). Well, I'm still not finish yet exploring Windows 7 Beta Build 7000 but this is the chance to get free and unlimited licenses number from Microsoft product. Gotta get it now.
Just a few minutes ago, I've read google news that Microsoft is already launch a new Microsoft Windows 7 Release Candidate (RC). Well, I'm still not finish yet exploring Windows 7 Beta Build 7000 but this is the chance to get free and unlimited licenses number from Microsoft product. Gotta get it now.To download Microsoft Windows 7 RC click here!
Sunday, May 3, 2009
Are you with Windows 7?

After 4 month of using Microsoft Windows 7 Ultimate, I think there is much more improvement compared with Windows Vista Ultimate. Only a few minor bugs I found on Start Menu and visual effect thing. Well, as I read a news from ComputerWorld, Windows 7 could be lunch this August but still no specific date. Hope it much better after the first release.
Windows 7 taskbar have totally different compare with other Windows version. When many Windows opened, taskbar will appear only an icon with a great stable thumbnail preview. Also, when user try to open many Windows Explorer, all the Windows will be grouped into one icon on the taskbar until user over their mouse cursor on it to choose which Window they want to use.
Well, here it is a few minor uncomfortable thing/bugs I found my self on Windows 7 Ultimate Beta Build 7000:
1. Start menu scroll bar some time cannot be scroll or dragged by mouse.
2. In some cases, the wallpaper disappear and leave only plain color.
3. When I lock the Windows and the logged in back, the screen resolution reset to the recommended setting (another rarely situation).
4. Some old application (mine was Macromedia Fireworks 8) still can't totally support Aero/transparent window effect.